Hack The Box - Socket
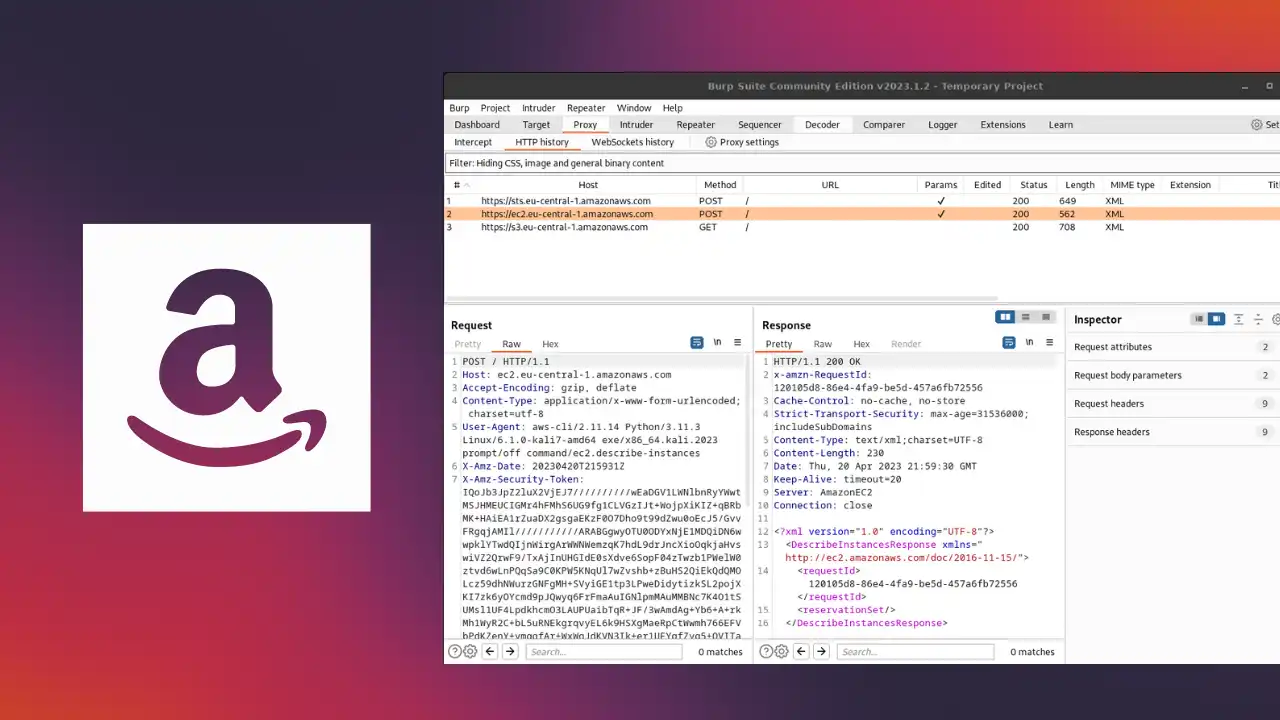
Socket is a Medium Difficulty Linux machine that requires reversing a Linux/Windows desktop application. This reveals an endpoint that is vulnerable to `SQL` injection via a websocket. Dumping the database leaks hashes that, once cracked, yield `SSH` access to the box. Finally, a `PyInstaller` script can be executed with elevated privileges that grant root access to the machine.